Legacy Security Information and Event Management (SIEM) is typically the solution for enterprises who need visibility into cyber threats across distributed IT infrastructure, essential to meeting regulatory compliance. However, SIEM solutions are cost-intensive, complex to properly configure, and cumbersome to maintain.
That’s why many companies are now migrating managed security service providers (MSSPs), such as Critical Path Security, who offer rapid deployment and through affordable subscription models.
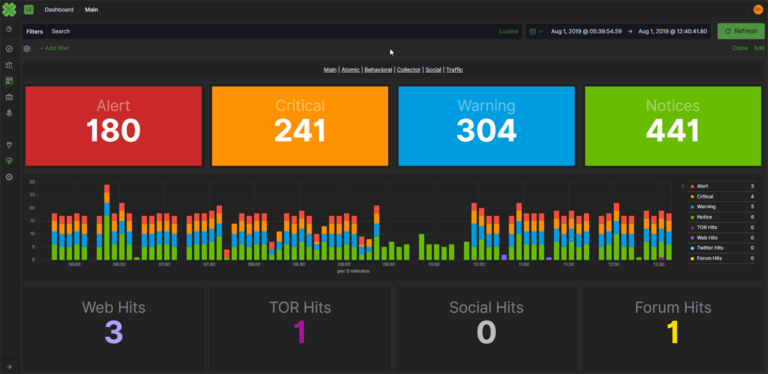
Managed Detection and Response (MDR) is a Critical Path Security managed security service that detects intrusions, malware, and malicious activity in your network and assists in responding quickly to eliminate and mitigate those threats.
Critical Path Security MDR services have a very light footprint on your network and use a combination of cybersecurity experts and advanced technology to eliminate false positives, identify real security threats, and develop actionable responses in real-time.
While the average time across industries to detect a compromise is over 200 days, Critical Path Security’s service regularly reduces that to moments and therefore minimizes the impact of a security event.
Critical Path Security MDR is a necessity for organizations that have a regulatory requirement to provide effective detection and response. Critical Path Security specializes in the delivery of these services to financial services, government, military subcontractors, retail, and energy.
Typically, these organizations struggle to recruit and retain in-demand security professionals. Unfortunately, these organizations are high-value targets for criminals, making an effective response that much more critical.
The Critical Path Security Services provides:
- Security experts who act as direct extensions of the organization
- 24/7 monitoring of events/logs, suspicious activity, and alerts
- Continuous multi-dimensional, multi-contextual network monitoring
- Incident Response Recommendations
- Ongoing Vulnerability Assessments
- Regulatory compliance reporting
