The following are examples how your organization can leverage the Critical Path Security Léargas Platform to solve real-world problems within an hour of reading this!
Please contact Critical Path Security to discuss your organization’s specific priorities.
Anomaly Detection
Is it an anomaly or a malicious threat? To make that determination advanced detection methods coupled with curated threat intelligence to identify whether an event is benign or a targeted attack. The Critical Path Security Léargas Platform provides notifications in context to reduce your MTTR and find threats that aren't revealed by traditional SIEM platforms.
Correlated Vulnerability Management Data
Having a full understanding of the risk you are attempting to mitigate is of utmost importance. Having Vulnerability Management Data directly correlated with network traffic and asset manifests isn't an option... it's a requirement.
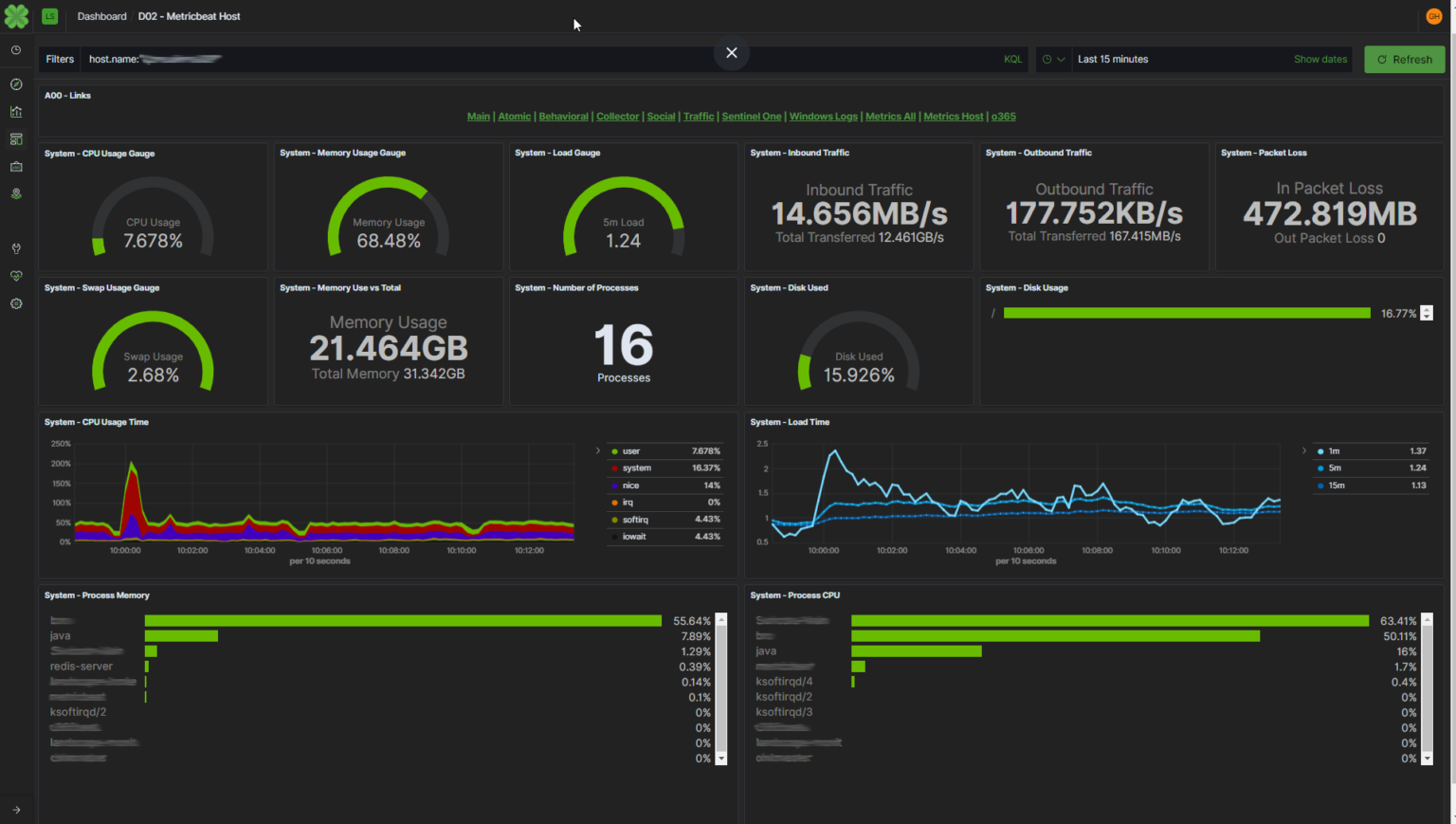
Interconnected Hybrid Network Visibility
Standalone monitoring tools used to gain visibility into locally or globally distributed network segments quickly becomes untenable. Organizations that leverage on-premise and cloud-based infrastructure need a different approach to ensure a strong security posture. Having operational and security data provided from a single vantage point lets you assess risk, reduce burden, and quickly respond to operational and security issues.
Work From Home
Pandemics have forever changed the landscape of the organization's networked systems. The Critical Path Security Léargas Platform enables you to visualize the interconnectedness of your entire environment, no matter where the devices and users may be. Don't stress. The Critical Path Security Léargas Platform enables your organization to visualize and analyze end-user and business impacts in real-time.
Data Exfiltration
The Critical Path Security Léargas Platform provides statistics associated with notable events that exhibit behaviors used in Data Exfiltration. The detections are effective regardless of data streams being encrypted or unencrypted.
Encrypted Traffic Investigation
Critical Path Security equipped with Zeek protocol analyzers and custom behavioral detections can provide valuable insight into events to enable response with encrypted protocols such as SSH, SSL, SMTP/TLS.
