
On September 4 of this year, the Office of the Assistant Secretary of Defense for Acquisition released its draft of the Cybersecurity Maturity Model Certification (CMMC) for public comment. The CMMC was created in response to growing concerns by Congress and the Department of Defense (DoD) over the increased presence of cyber threats and intrusions aimed at the Defense Industrial Base (DIB) and its supply chains.
The increase of successful Cybersecurity attacks against Defense Contractors and Subcontractors has been on a steady climb over the past years, leading to direct intervention and the creation of the CMMC.
It is the duty of the manufacturer to monitor their environment, implement effective security controls, and ensure that critical systems are protected from malicious activities, such as ransomware, malware, etc. The protection of intellectual property associated with government projects is of most importance.
Unfortunately, a recent investigation into Boeing's infrastructure has illuminated vulnerabilities that are present across nearly all contractors and subcontractors. The more egregious lapses in their security posture are outlined below.
A lack of a TLS certification for encrypted communication was missing on the public web server. This is a direct requirement of "System and Communications Protection" in the CMMC. Without encrypted communications, leveraging a TLS certificate, an opportunity to inject malware into web traffic and potentially introduce malware exists.
In comparison, greater than 90% of public web traffic is encrypted.
Additionally, Boeing email server's also lack of a Domain-based Message Authentication, Reporting and Conformance (DMARC) record has led to several successful phishing attacks and recorded delivery of multiple strains of malware. Department of Homeland Security (DHS) required all federal agencies to implement a DMARC record starting in January 2018.
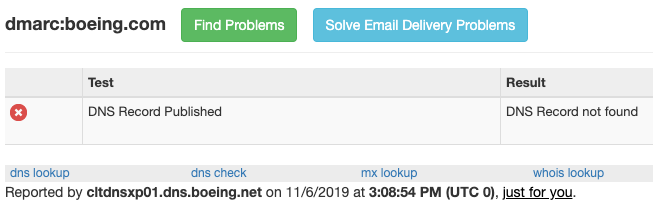
Without a DMARC record, an attacker could forge a legitimate-looking email from any Boeing employee, including the CEO, that would use the boeing.com and associated domains and request a targeted user to open a malicious attachment containing malware or request sensitive information. A DMARC could prevent such an attack. Configuring DMARC records is a relatively small task for a qualified security professional.
Boeing domains were used in trafficking malware as recently as October 28th of 2019. More than 40 different files containing malware have been observed in the wild.
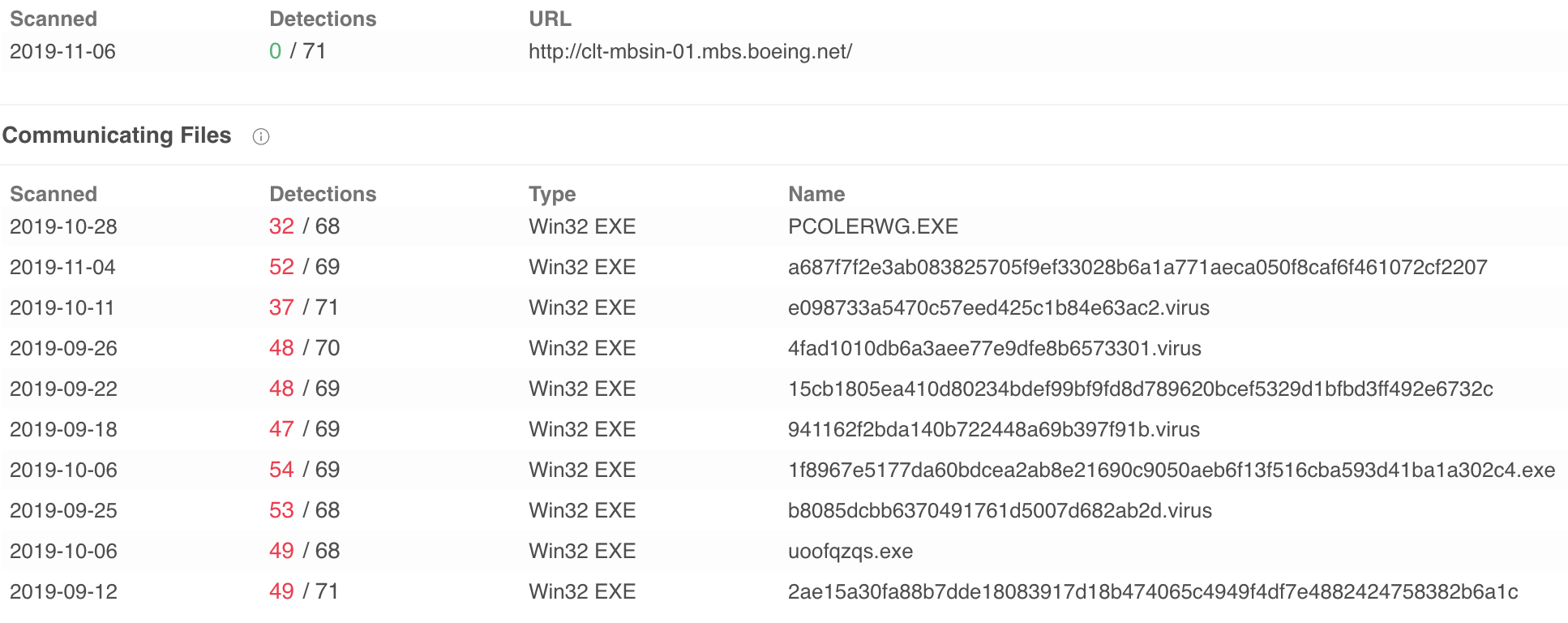
With such a high amount of malware being trafficked, combined with the lack of basic controls, there is a high probability that the server is being used to exfiltrate sensitive information associated with both civilian and government initiatives.
The Aviation ID portal, provided by Exostar, was also found to be vulnerable to several cross-site scripting (XSS) attacks. CSO Online states that "poor credential and authentication standards". However, Critical Path Security did not verify these findings. Patrick Kelley, the founder of Critical Path Security, is quoted as stating...
In the 15 years of working directly with Exostar in support of aerospace subcontractors, I've experienced several occurrences of failed implementations of security controls in platforms, namely with their SharePoint-based solutions. For quite some time, subcontractors would find ways to operate outside of the platforms, due to operational failures, and lack of proper rights to access necessary data.
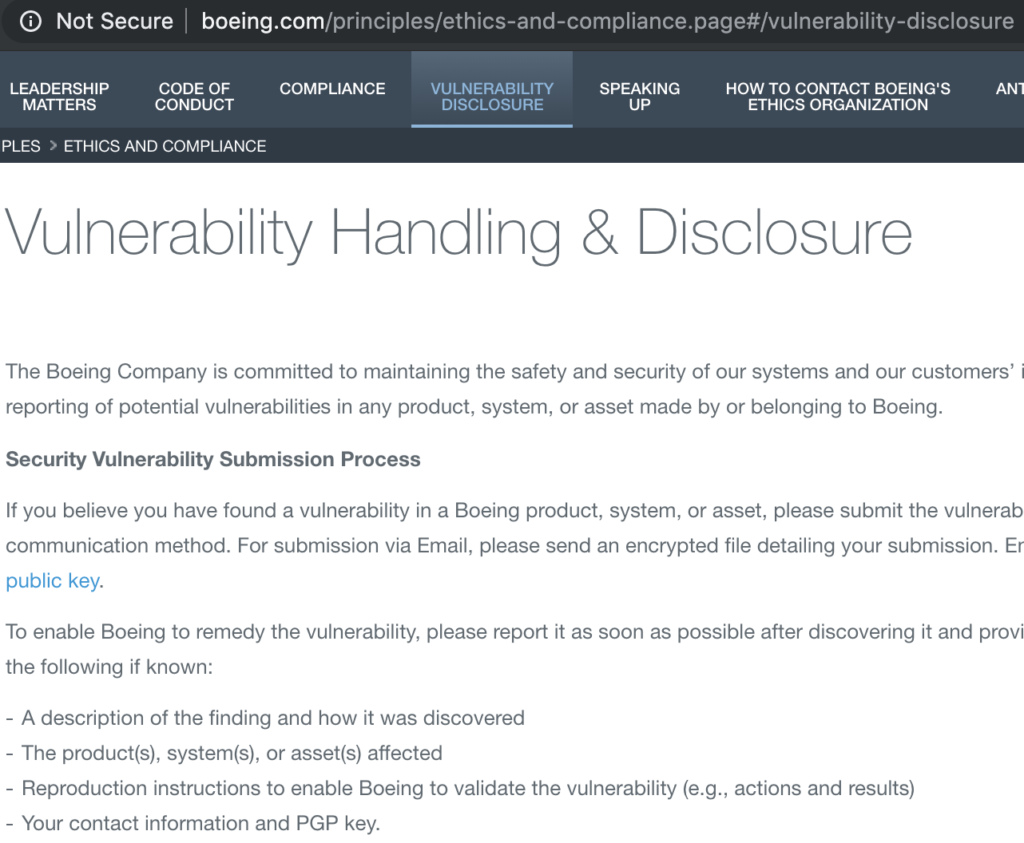
Critical Path Security was able to confirm that the Boeing Vulnerability Disclosure Program (VDP) was utilizing encryption and the offered Pretty Good Privacy (PGP) key that could not be properly installed.
This is very troubling as sensitive information, often containing undisclosed vulnerabilities, is often communicated using these channels. Without proper validation of recipients and encrypted communications, this information could easily end up in the wrong hands.
It is important to understand that these findings are very common. Critical Path Security found public-facing vulnerabilities in nearly every subcontractor that researched. It is imperative that organizations quickly get a grasp of their security vulnerabilities and remediate them, immediately.
Unlike NIST SP 800-171, which is implemented through a regulation — i.e., Defense Federal Acquisition Regulation Supplement (DFARS) clause 252.204-7012 — (DoD) plans to implement the requirements of the model on a purely contractual basis. The required CMMC level applicable to procurement will be listed in the solicitation in sections L and M and will be a “go/no-go decision.”
However...
For organizations that fail to fully comply, DFARS 252.204-7009(b)(5) states that disregard of these requirements can lead to other criminal, civil, administrative, or contract penalties.
These consequences may include:
Breach of Contract damages
False Claims Act damages
Liquidated Damages
Termination for Default
Termination for Convenience
Suspension
The events surrounding Boeing shine a bright light into the operations of smaller contractors and subcontractors. The lack of significant resources to defend from the ever-growing threats place these organizations in precarious situations.
For many small DoD contractors, the most effective way to meet the requirements of DFARS is to engage a Managed Security Service Provider (MSSP), such as Critical Path Security. Remember that contractors carry the responsibility for ensuring that their company meets the DFARS requirements. So, it is essential to choose an MSSP that is competent and trustworthy.
By outsourcing the DFARS/CMMC Compliance work to a qualified provider, DoD contractors will save effort and money getting and staying compliant. An outsourced provider will have all of the required document templates for the Gap Analysis and the System Security Plan. Critical Path Security can also provide ongoing monitoring and response to threats. Critical Path Security maintains strong Managed IT (MSP) relationships who have the resources required to perform the remediation steps required to become compliant and the legal documentation to prove compliance.
If you are unsure about where you stand, call us today! Initial consultations are always free.
