AI-POWERED
EXTENDED DETECTION & RESPONSE
Empowering your organization to proactively detect, investigate, and block security threats.
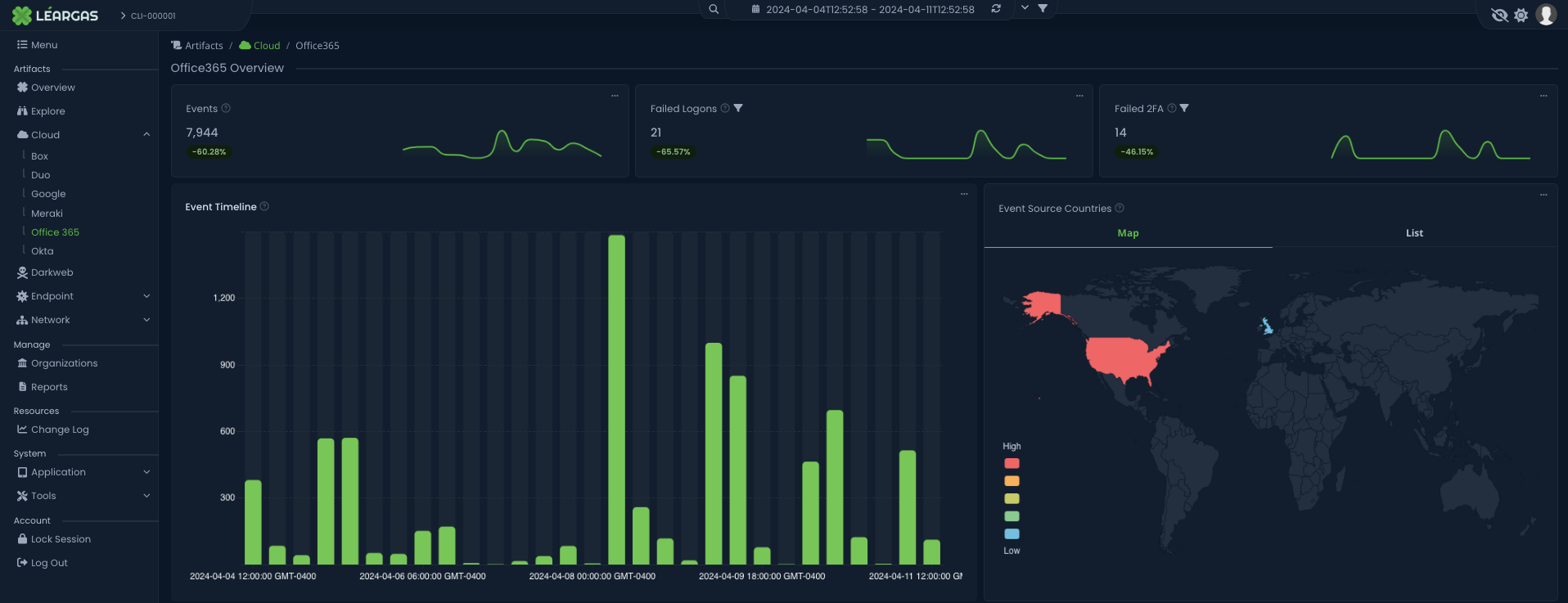
LÉARGAS XDR WITH GENERATIVE AI
The Léargas XDR Platform with Generative AI is your all-in-one cybersecurity solution, providing a comprehensive arsenal for your team.
From Threat Intelligence to Deception Technology and Network Traffic Analysis, we equip you with everything you need for unmatched visibility across your entire infrastructure in real-time, 24/7.
The Léargas XDR Platform is meticulously designed for efficiency and scalability. It can be deployed in just one day, eliminating the need for 100+ hours of upfront professional services or multiple licenses across various platforms. This seamless adaptability ensures that Léargas XDR Platform easily grows with your organization's evolving needs.
Whether it's today or tomorrow, you can count on Léargas to deliver what you need, precisely when you need it.

YOUR STRATEGIC ADVANTAGE AGAINST DIGITAL THREATS
WHY LÉARGAS IS YOUR PREMIER CHOICE FOR CYBERSECURITY
COMMANDING SECURITY ASSURANCE
Léargas is an all-in-one XDR, Vulnerability Assessment, and SIEM solution for IT and OT Industrial Control Systems, On-Premise, and Cloud environments. The centralized platform monitors all layers of infrastructure in real-time.
BUDGET-CONSCIOUS INFRASTRUCTURE PROTECTION
Léargas understands that you may have limited budget and resources. In order to secure our nation's most critical infrastructure and data, we have created a comprehensive solution that scales to protect all assets and data with a price structure that is attainable for even the smallest EMC, rural government, or corporation.
POWERFUL AI, COST-EFFECTIVE OUTCOMES
Leveraging our AI tools means fortifying your defenses with expertise on par with a Senior Security Analyst valued at $135,000 or more. This formidable advantage safeguards your digital assets, keeps you ahead of threats, and ensures your organization's cybersecurity resilience.
STREAMLINED SECURITY VS. COSTLY ALTERNATIVES
Piecemealing various solutions together causes inefficient information sharing and a lack of actionable insight into rapidly evolving attacks. The combined cost to attempt to replicate Léargas protection starts at $955,000 per year not including the staff required to manage a disjointed approach.
SATISFY MANDATES, ENSURE COMPLIANCE
Positioned as a guardian of your cybersecurity framework, Léargas diligently meets the stringent criteria set forth by governing bodies, aligning seamlessly with standards such as NIST, PCI, PIPEDA, and SOC2. This assures robust defense against cyber threats and serves to fortify your standing in terms of regulatory compliance.
SWIFT DEPLOYMENT, INSTANT DEFENSE
Rapid Deployment is more than just a feature; it's instant security readiness. With Léargas, you can activate subscriptions in as little as 30 minutes. This means you can swiftly bolster your defenses and respond to emerging threats with agility, ensuring your organization remains resilient in the face of evolving cybersecurity challenges.
MORE FROM THE BLOG
TRUST & EXECUTION
WHAT OUR CUSTOMERS THINK
"We have been customers of Léargas Security for several years now. The professionalism and care shown by the entire team has been excellent. As the manager over a small IT Department for a rural electric utility, time and manpower is a precious commodity. Léargas Security’s skilled staff and platform provides a level of security that I could not otherwise achieve. I have contracted with other security operations centers before, but none have been as responsive, alert, and knowledgeable as the engineers and staff at Leargas."
Michael M.
Electric Cooperative
“I’ve been extremely pleased with the relationship we have formed with the employees of Léargas Security. They are very professional and have done a very thorough job of working with us to protect our systems. The daily reports are very detailed and I really appreciate the monthly updates. They do a really good job of working with our employees and third-party vendors."
Steve S.
Government
“I can honestly say that working with Léargas has given our IT staff the peace of mind to sleep soundly knowing that we have a dedicated Security Expert watching our backs 24/7. This is a no-brainer and money well spent as far as we are concerned. I am thankful daily that we found Léargas."
Herman T.
Electric Cooperative
"Léargas Security has exceeded our expectations with their dedicated support and unwavering commitment to securing our organization. I am able to sleep well at night knowing they have my back."
Daniel S.
Government
AS FEATURED ON





SCHEDULE YOUR LÉARGAS XDR DEMO NOW
Take a proactive stance in safeguarding your digital assets.
SOLUTIONS FOR ANY SECTOR
Tailored Security Excellence for EMCs, Enterprises, Government, and MSSPs
Whether you're an Enterprise seeking fortified defenses, a Government entity safeguarding national interests, an EMC with vital assets to protect, or an MSSP looking to empower clients with cutting-edge security, Léargas has crafted specialized solutions for you.
© Copyright Léargas Security. All Rights Reserved.